简单说明:
1、mkcert 是一个用于在本地开发环境中创建受信任的https证书的工具。
2、mkcert通过自动创建并安装一个本地的证书颁发机构(CA)到系统和浏览器的信任库中,解决了传统自签名证书带来的浏览器安全警告问题。
3、在 Linux 环境下,nginx 部署 mkcert 创建的本地受信任的https证书是一个非常实用的配置,在本地或内网通过https访问服务,浏览器不会显示“不安全”的警告。
4、整个过程可以分为四个主要步骤:安装 mkcert、生成本地 CA 和服务器证书、配置 Nginx,以及在客户端建立信任。
安装前准备:
1、防火墙配置
Rocky Linux默认使用的是firewall作为防火墙
firewall-cmd --list-all #显示所有规则(含服务、端口、区域)
systemctl status firewalld #检查 firewalld 状态
#开放80 443 端口
firewall-cmd --permanent --add-port=80/tcp
firewall-cmd --permanent --add-port=443/tcp
firewall-cmd --reload #重新加载防火墙配置
2、关闭SELINUX
vi /etc/selinux/config
#SELINUX=enforcing #注释掉
#SELINUXTYPE=targeted #注释掉
SELINUX=disabled #增加
:wq! #保存退出
setenforce 0 #使配置立即生效
getenforce #查看 SELinux 当前运行模式
3、安装编译工具包
yum install tar make gcc gcc-c++ perl pcre2-devel zlib-devel glibc-devel
具体操作:
1、安装mkcert
1.1安装依赖包,mkcert需要nss-tools (CentOS/RHEL) 或 libnss3-tools (Ubuntu/Debian) 来管理浏览器的信任库
yum install nss-tools
1.2下载并安装mkcert
下载地址:
https://dl.filippo.io/mkcert/latest?for=linux/amd64
https://github.com/FiloSottile/mkcert
https://github.com/FiloSottile/mkcert/releases/download/v1.4.4/mkcert-v1.4.4-linux-amd64
# 下载最新版本 (请根据你的系统架构选择,此处以 linux-amd64 为例)
curl -JLO "https://dl.filippo.io/mkcert/latest?for=linux/amd64"
# 赋予执行权限
chmod +x mkcert-v*-linux-amd64
# 拷贝到系统路径,使其成为全局命令
cp mkcert-v*-linux-amd64 /usr/local/bin/mkcert
# 验证安装是否成功
mkcert -version
2、生成 CA 和服务器证书
2.1创建并安装本地 CA,这个命令会创建一个本地 CA,并将其自动添加到系统的信任库中
mkcert -install
#成功执行后,会看到如下提示
Created a new local CA
The local CA is now installed in the system trust store!
2.2生成服务器证书
# 请将下面的 your_server_ip_or_domain 替换为你实际的内网 IP(如 192.168.1.100)或自定义域名(如 myapp.local)。
# 可以同时指定多个域名或IP,例如 localhost 和你的内网IP
# mkcert your_server_ip_or_domain localhost 127.0.0.1
mkdir -p /root/cert #创建证书存放目录
cd /root/cert
mkcert 192.168.21.11 localhost 127.0.0.1
Created a new certificate valid for the following names
- "192.168.21.11"
- "localhost"
- "127.0.0.1"
The certificate is at "./192.168.21.11+1.pem" and the key at "./192.168.21.11+1-key.pem"
It will expire on 28 July 2028
#重命名证书和私钥
mv 192.168.21.11+1.pem server.crt
mv 192.168.21.11+1-key.pem server.key
3、配置 Nginx
3.1安装nginx
3.1.1 安装包下载:
① nginx
https://nginx.org/download/nginx-1.30.0.tar.gz
② zlib
https://www.zlib.net/zlib-1.3.2.tar.gz
③ pcre2
https://github.com/PCRE2Project/pcre2/releases/download/pcre2-10.47/pcre2-10.47.tar.gz
④ openssl
https://github.com/openssl/openssl/releases/download/openssl-3.5.6/openssl-3.5.6.tar.gz
3.1.2 创建nginx安装目录
mkdir -p /data/server/nginx
mkdir -p /data/server/nginx/packages
mkdir -p /data/server/nginx/install
上传安装包到/data/server/nginx/packages目录
3.1.3 安装nginx
#解压pcre
cd /data/server/nginx/packages
tar zxvf pcre2-10.47.tar.gz
#解压zlib
cd /data/server/nginx/packages
tar zxvf zlib-1.3.2.tar.gz
#解压openssl
cd /data/server/nginx/packages
tar zxvf openssl-3.5.6.tar.gz
#安装nginx
#nginx默认运行账号和组是Linux系统的内置账号和组nobody
#创建nginx运行账号和组
groupadd www
useradd -g www www -s /sbin/nologin
cd /data/server/nginx/packages
tar zxvf nginx-1.30.0.tar.gz
cd nginx-1.30.0
./configure \
--prefix=/data/server/nginx \
--user=www \
--group=www \
--without-http_memcached_module \
--with-http_stub_status_module \
--with-http_ssl_module \
--with-http_v2_module \
--with-http_gzip_static_module \
--with-http_realip_module \
--with-stream \
--with-stream_ssl_preread_module \
--with-stream_ssl_module \
--with-http_flv_module \
--with-http_mp4_module \
--with-http_sub_module \
--http-client-body-temp-path=/data/server/nginx/client \
--http-proxy-temp-path=/data/server/nginx/proxy \
--http-fastcgi-temp-path=/data/server/nginx/fcgi \
--http-uwsgi-temp-path=/data/server/nginx/uwsgi \
--with-openssl=/data/server/nginx/packages/openssl-3.5.6 \
--with-zlib=/data/server/nginx/packages/zlib-1.3.2 \
--with-pcre=/data/server/nginx/packages/pcre2-10.47
make -j$(nproc)
make install
#查看nginx版本和安装模块信息
/data/server/nginx/sbin/nginx -V
3.1.4 配置nginx启动脚本
vi /data/server/nginx/nginx.sh
#!/bin/bash
NGINX_PATH="/data/server/nginx/sbin/nginx"
PID_FILE="/data/server/nginx/logs/nginx.pid"
function start_nginx() {
if [ -f $PID_FILE ]; then
echo "Nginx is already running."
else
echo "Starting Nginx..."
$NGINX_PATH
echo "Nginx started."
fi
}
function stop_nginx() {
if [ -f $PID_FILE ]; then
echo "Stopping Nginx..."
$NGINX_PATH -s stop
echo "Nginx stopped."
else
echo "Nginx is not running."
fi
}
function restart_nginx() {
if [ -f $PID_FILE ]; then
echo "Restarting Nginx..."
$NGINX_PATH -s stop
sleep 1
$NGINX_PATH
echo "Nginx restarted."
else
echo "Nginx is not running. Starting it now..."
$NGINX_PATH
echo "Nginx started."
fi
}
function reload_nginx() {
if [ -f $PID_FILE ]; then
echo "Reloading Nginx configuration..."
$NGINX_PATH -s reload
echo "Nginx configuration reloaded."
else
echo "Nginx is not running. Cannot reload the configuration."
fi
}
function status_nginx() {
if [ -f $PID_FILE ]; then
echo "Nginx is running with PID $(cat $PID_FILE)."
else
echo "Nginx is stopped."
fi
}
case "$1" in
start)
start_nginx
;;
stop)
stop_nginx
;;
restart)
restart_nginx
;;
reload)
reload_nginx
;;
status)
status_nginx
;;
*)
echo "Usage: $0 {start|stop|restart|reload|status}"
exit 1
;;
esac
:wq! #保存退出
#添加执行权限
chmod +x /data/server/nginx/nginx.sh
#启动命令
/data/server/nginx/nginx.sh start
3.1.5 使用systemd服务实现nginx开机启动
vi /lib/systemd/system/nginx.service #添加以下代码
[Unit]
Description=The NGINX HTTP and reverse proxy server
After=syslog.target network.target remote-fs.target nss-lookup.target
[Service]
Type=forking
PIDFile=/data/server/nginx/logs/nginx.pid
ExecStartPre=/data/server/nginx/sbin/nginx -t
ExecStart=/data/server/nginx/sbin/nginx
ExecReload=/data/server/nginx/sbin/nginx -s reload
ExecStop=/bin/kill -s QUIT $MAINPID
ExecStartPost=/bin/sleep 0.1
PrivateTmp=true
[Install]
WantedBy=multi-user.target
:wq! #保存退出
/data/server/nginx/sbin/nginx -s stop #停止
systemctl daemon-reload #重载 systemd 配置
systemctl enable nginx.service #设置开机自启动
systemctl start nginx.service #启动
systemctl stop nginx.service #关闭
systemctl restart nginx.service #重启
systemctl reload nginx.service #重新加载配置文件
3.1.6 修改nginx配置文件,让它使用刚刚生成的证书
#创建证书存放目录
mkdir -p /data/server/nginx/conf/cert/
#拷贝证书
cp /root/cert/server.crt /data/server/nginx/conf/cert/
cp /root/cert/server.key /data/server/nginx/conf/cert/
#备份默认配置文件
cp /data/server/nginx/conf/nginx.conf /data/server/nginx/conf/nginx.conf.default.bak
#创建目录
mkdir -p /data/server/nginx/conf/stream/
mkdir -p /data/server/nginx/conf/upstream
mkdir -p /data/server/nginx/conf/vhosts
vi /data/server/nginx/conf/nginx.conf
user www;
worker_processes auto;
worker_cpu_affinity auto;
worker_rlimit_nofile 65535;
error_log /data/server/nginx/logs/error.log notice;
pid /data/server/nginx/logs/nginx.pid;
events {
worker_connections 65535;
use epoll;
multi_accept on;
}
stream{
include /data/server/nginx/conf/stream/*conf;
}
http {
include mime.types;
default_type application/octet-stream;
log_format main '$remote_addr - $remote_user [$time_local] "$request" '
'$status $body_bytes_sent "$http_referer" "$http_user_agent" '
'"$http_x_forwarded_for" "$upstream_cache_status" $upstream_response_time $request_time';
log_format awstats '$remote_addr - $remote_user [$time_local] "$request" '
'$status $body_bytes_sent "$http_referer" '
'"$http_user_agent" "$http_x_forwarded_for"';
access_log logs/access.log main;
#access_log off;
charset UTF-8;
server_names_hash_bucket_size 128;
client_header_buffer_size 32k;
large_client_header_buffers 4 32k;
client_max_body_size 10000m;
sendfile on;
tcp_nopush on;
keepalive_timeout 60;
tcp_nodelay on;
server_tokens off;
fastcgi_connect_timeout 300;
fastcgi_send_timeout 300;
fastcgi_read_timeout 300;
fastcgi_buffer_size 128k;
fastcgi_buffers 4 128k;
fastcgi_busy_buffers_size 256k;
fastcgi_temp_file_write_size 256k;
fastcgi_intercept_errors on;
client_header_timeout 3m;
client_body_timeout 3m;
send_timeout 3m;
connection_pool_size 256;
request_pool_size 4k;
output_buffers 4 32k;
postpone_output 1460;
client_body_buffer_size 512k;
gzip on;
gzip_min_length 1k;
gzip_buffers 4 16k;
gzip_http_version 1.0;
gzip_comp_level 3;
gzip_proxied any;
gzip_types text/plain application/x-javascript application/javascript application/json text/css text/javascript application/xml image/gif image/png image/jpg image/jpeg;
gzip_vary on;
proxy_connect_timeout 300;
proxy_read_timeout 300;
proxy_send_timeout 300;
proxy_buffers 4 64k;
proxy_busy_buffers_size 128k;
proxy_temp_file_write_size 128k;
proxy_http_version 1.1;
proxy_set_header Connection "";
proxy_ignore_client_abort on;
proxy_intercept_errors on;
proxy_next_upstream error;
proxy_buffer_size 64k;
proxy_temp_path /data/server/nginx/nginx_cache 1 2;
proxy_cache_path /data/server/nginx/nginx_proxy_cache levels=1:2 keys_zone=cache_one:128m inactive=2d max_size=128m;
proxy_pass_header Set-Cookie;
map $http_upgrade $connection_upgrade {
default upgrade;
'' close;
}
include upstream/*.conf;
include vhosts/*.conf;
}
:wq! #保存退出
vi /data/server/nginx/conf/vhosts/default.conf
server {
# 监听 443 端口,开启 SSL 和 HTTP/2
listen 443 ssl;
http2 on;
server_name _;
# --- SSL 证书配置 (已填入你的路径) ---
ssl_certificate /data/server/nginx/conf/cert/server.crt;
ssl_certificate_key /data/server/nginx/conf/cert/server.key;
# --- SSL 安全加固配置 ---
# 推荐只使用 TLSv1.2 和 TLSv1.3
ssl_protocols TLSv1.2 TLSv1.3;
# 推荐加密套件
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-CHACHA20-POLY1305;
ssl_prefer_server_ciphers off;
# 会话缓存优化
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 10m;
root /data/server/nginx/wwwroot/default;
index index.html index.htm;
access_log /data/server/nginx/logs/default.log main;
}
:wq! #保存退出
mkdir -p /data/server/nginx/wwwroot/default
vi /data/server/nginx/wwwroot/default/index.html
Thank you for using nginx
:wq! #保存退出
systemctl restart nginx.service #重启
#下载根证书并安装
mkcert -CAROOT #查找根证书
ls -l /root/.local/share/mkcert
-r--------. 1 root root 2484 Apr 28 16:53 rootCA-key.pem
-rw-r--r--. 1 root root 1761 Apr 28 16:53 rootCA.pem
根证书是rootCA.pem
下载这个文件到自己的电脑并安装
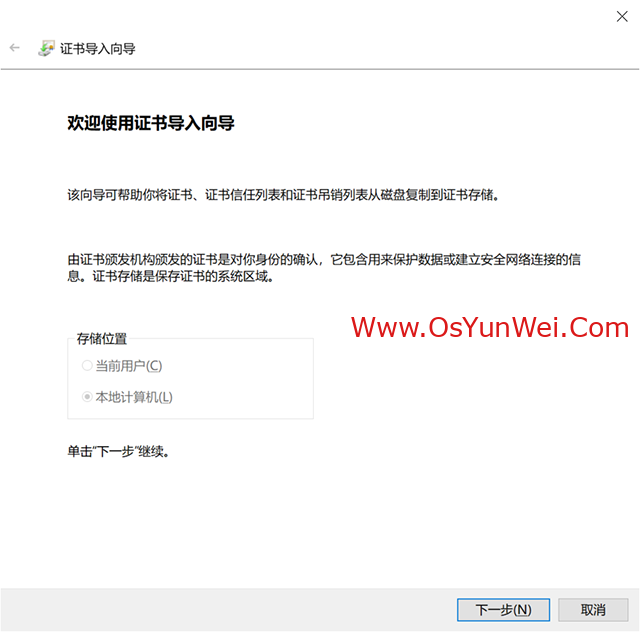
强制存入本地计算机:
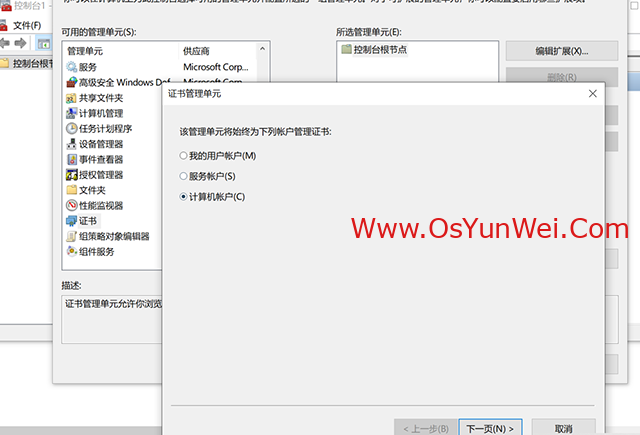
1.按 Win + R 键,输入 mmc,回车。
2.点击菜单栏 “文件” -> “添加/删除管理单元...”。
3.在左侧列表中找到 “证书”,选中它,点击中间的 “添加 >”。
【关键一步】 在弹出的窗口中,一定要选“计算机账户(Computer account)”(千万别选默认的“我的用户账户”)。
点“下一步” -> 选 “本地计算机” -> 完成 -> 确定。
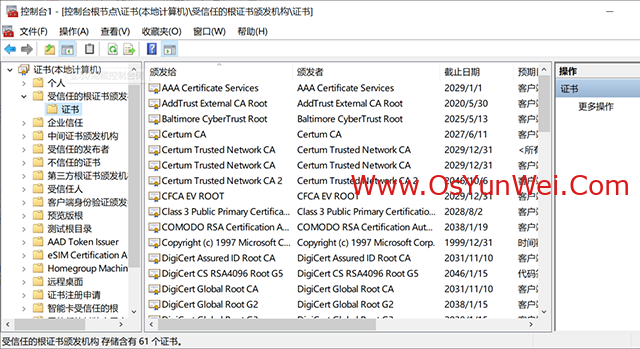
4.在控制台左侧依次展开:证书(本地计算机) -> 受信任的根证书颁发机构 -> 证书。
在右侧空白处右键 -> 所有任务 -> 导入...。
选择你桌面上的 rootCA.pem(或 .crt),一直点下一步直到完成。
彻底关闭浏览器(右下角托盘也要退出),重新打开尝试。

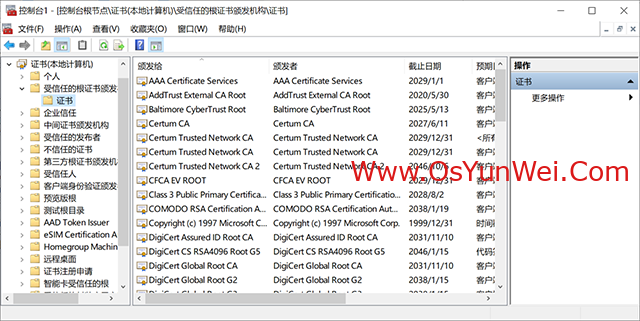
5.浏览器打开https://192.168.21.11/

现在已经显示证书安全了.
至此,Linux下nginx使用mkcert创建的https证书完成。

 ②190706903
②190706903  ③203744115
③203744115